Tenable today announced a solution designed to reduce cybersecurity risk across today's converged IT/OT (operational technology) environments.
Enhancements to the Tenable.io platform and Industrial Security, an asset discovery and vulnerability detection solution for Operational Technology (OT) systems, delivered in partnership with Siemens, enable organisations to manage cyber exposure holistically across IT and OT and prioritise remediation based on the criticality of the asset and the vulnerability. OT and critical infrastructure systems were initially designed to work in isolation from the network and walled off from outside cybersecurity threats.
But digital transformation has turned these once-isolated systems into connected devices, making them high-value targets for attackers.
In fact, attacks on OT assets often start by compromising IT systems and then moving laterally, as noted in the FBI and Department of Homeland Security issued an unprecedented warning about Russian state-sponsored attacks on US critical infrastructure.
Converged environments contain a mix of IT and OT devices and systems that demand a holistic approach to cybersecurity so that organisations can accurately manage, measure and reduce cybersecurity risk. Enhancements include:
- Smart Scanning: Smart scanning builds an intelligence layer on top of active scanning and passive network monitoring to assess IT and OT systems within a single workflow. In certain situations, active scanning may be too intrusive for sensitive OT systems and can cause system disruption if performed on these devices. Smart Scanning will stop actively scanning IT assets when it identifies them as OT devices.
- Expanded OT Asset Coverage: Tenable has expanded its assessment capabilities across an even broader range of OT assets. Expanded support includes over 250 additional devices and applications from Siemens, Schneider and Rockwell/Allen-Bradley, providing customers with broader visibility across their OT assets and mixed IT/OT technology environments.
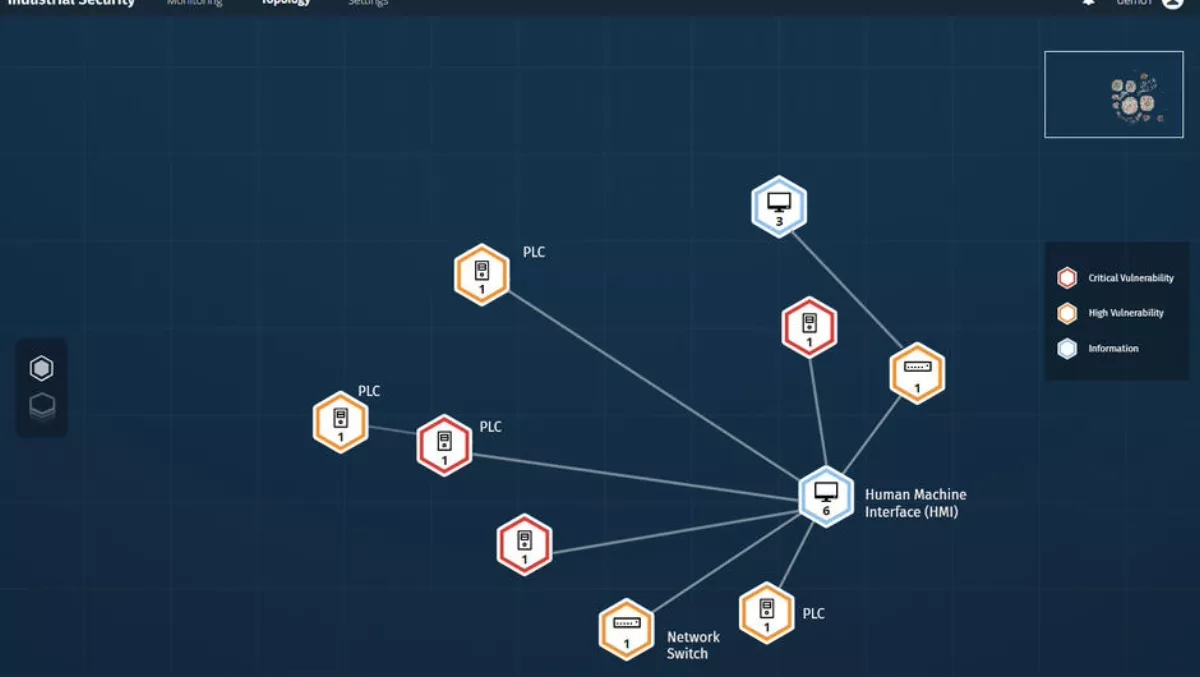
- Interactive Topology Maps: New 2D and 3D topology maps display the relationships between IT and OT assets as part of a converged system. This new level of IT and OT asset intelligence combined with our deep vulnerability intelligence provide customers with a risk-based heat map based on the criticality of the asset and the vulnerability, enabling more efficient prioritisation and faster remediation.
“The security challenges facing organisations with operational technologies cannot be overstated,” says Tenable chief product officer Dave Cole.
“IT and OT assets individually - and together as converged systems - comprise part of the modern attack surface, and are therefore points of cybersecurity risk. Organisations that approach understanding their state of security by neglecting to view OT assets as part of the attack surface lack critical visibility required to understand their Cyber Exposure,
“With Tenable.io, including our Industrial Security offering purpose-built for OT Security, Tenable is uniquely breaking down silos, providing a unified view of Cyber Exposure across converged IT/OT environments.” The announcement comes on the back of the Tenable Research team's discovery of a critical remote code execution vulnerability in two Schneider Electric applications used in manufacturing, oil and gas, water, automation and wind and solar power facilities and underscores the company's commitment to pioneering solutions for cybersecurity for OT and critical infrastructure.
